
Risk Mitigation
As mentioned in the section on the overall cybersecurity risk management process, there are four essential steps in risk management:
- Identify risks
- Assess risks
- Identify possible mitigation measures
- Decide what to do about the residual risk
After identifying your risks and assessing them (that is, their impact and likelihood of occurring), then the next step is to see what you can do about them – that is, whether and how you can mitigate those risks.
As you can imagine, the type of mitigation depends on the type of threat. If you are threatened by ransomware, then the mitigation measures might involve specialized ransomware virus detection software, as well as training for personnel about dangerous email attachments. If you are threatened by insider attacks, then a completely different set of measures is applicable.
But even before thinking about specific measures, there is another consideration. In cybersecurity, as in life in general, there is a need to balance the application of prevention versus detection and recovery. Often prevention is the best and simplest mitigation measure. To avoid lung cancer, don’t smoke – it’s cheap and effective. But sometimes prevention is either infeasible or not worth the cost. To avoid car accidents, don’t drive – very effective, but generally infeasible.
When prevention is infeasible or too expensive, an alternative measure is to accept the possibility that the incident will happen, but to mitigate the consequences. You have to accept the possibility that one of your disks will crash and lose all of its data – but you can mitigate the consequences through regular backups (recovery).
How do you decide which to adopt? One clue is given by the mix of impact and likelihood. When the impact and likelihood are both high, then a mix of prevention and detection is generally a good idea. But there are also situations in which the impact is high but the likelihood is low. A disk crash falls into that category. In cases like that, the most cost-effective solution is often to concentrate only on detection and recovery.
This approach of combined prevention and detection/recovery is embodied in the NIST Cybersecurity Framework.
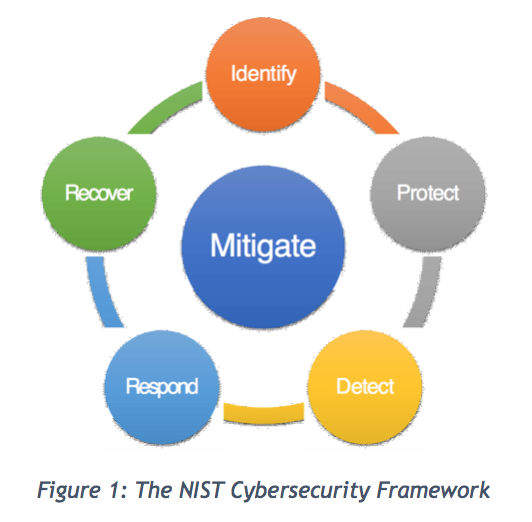
The framework helps you to organize your thinking about how to adopt mitigation measures in terms of prevention versus detection/recovery.
The second dimension of mitigation is technical measures versus procedural measures (best practices). Here are some typical recommendations for small businesses, courtesy of the National Institute of Standards and Technology.
- Identify. This is an aspect of prevention. Identify who has access to your information and control over it. Identify your employees – do background checks (this is a way of preventing insider attacks). Identify who is doing what by, say, making sure that each employee has their own individual account.
- Protect. We are still dealing with prevention here. Limit unnecessary employee access to information. This mitigates the possibility of insider attacks, and also innocent mishandling of data. Install surge protectors and universal power supplies. This is a good example of a technical measure. More technical examples include continuous security updates for software, using cryptography, and hardware firewalls. A final (very important!) example is employee training – this falls into the category of “best practices”.
- Detect. Now we move into the area of detection. Virus and malware detection software fall into this category (technical). Good log-keeping facilities can also help in the detection of intrusions (best practice).
- Respond. We are still in the area of detection / recovery now. When an incident has occurred, your readiness to respond will have an effect on how much of the damage is mitigated. These measures fall mostly into the “best practices” category: determining who has responsibility for coordinating the response; determining what to do (e.g. shut down all computers); determining who to notify (including the police or even the FBI if you suspect something more serious).
- Recovery. Here we remain in the area of detection and recovery. One classic technical mechanism is making backups of your data. A good example of “best practice” procedures is some form of “lessons learned” and “continuous improvement” so that you learn from the incident and ensure that it doesn’t happen again.
It is the mission of cyberwatching.eu to help provide you with the information you need to evaluate the many possibilities for risk mitigation.
At this point, you have the unwelcome task of estimating your residual risk after all of your mitigation mechanisms have been put into place. This is never an easy task, and here, too, the expertise of professionals will be useful for helping to put numbers on the estimated risk. This is also where the growing number of incident databases will help, as the community sees what the costs of cyber incidents have been for organizations and what the costs could be for you due to the residual risk you must confront.
News
On the event of the adoption of the draft regulation laying down measures for a high common level of cybersecurity at the institutions, bodies, offices and agencies of the Union, the AI4HealthSec project kicked off a process to provide its opinion.
Resources for EU Research
Resources for SMEs
News & Events
Reports
Cyberwatching.eu has received funding from the European Union’s Horizon 2020 research and innovation programme under grant agreement No 740129. The content of this website does not represent the opinion of the European Commission, and the European Commission is not responsible for any use that might be made of such content. Privacy Policy | Disclaimer / Terms and Conditions of Use
