
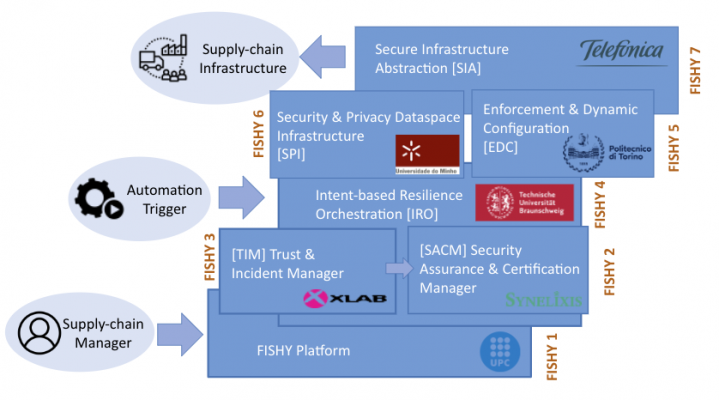
FISHY Key Technologies
Date:
09/05/2022
KER1 Dashboard & Platform
Functionality: Easing FISHY platform usability, making the whole system user-friendly and ready to be used for different users according to their expected profile and thus permitted functionalities.
Benefits: Enhanced customer experience: Easy access to the supply chain cybersecurity in a single window with meaningful and useful output
Differentiator: Frontend designed to support the specific needs inherent to the heterogeneous and diverse supply chain scenario also supporting the hybrid model FISHY is envisioned to support.
KER2 Vulnerability Forecast & Risk Estimation (TIM)
Functionality: Monitoring and gathering metrics from supply chain infrastructure, performing analysis, raising alerts, proposing mitigation actions
Benefits: Combination of multiple different tools (vuln. estimation, IDS, SIEM, ...) to provide as large of coverage of cybersecurity as possible.
Differentiator: Architecture designed for supply chains, instead of a single network.
KER3 Intent-based Resilience Orchestration (IRO)
Functionality: Automation of the interactions between the user defining high-level intents and the system applying high-level policies.
Benefits: The user does not need to know the intermediate technical steps to perform an intent.
Differentiator: Solution translating high-level intents into configured policies, and interacting with the system response using AI techniques.
KER4 Security Assurance and Certification Manager (SACM)
Functionality: Auditing and reasoning security metrics tailored to the pilots' infrastructure, and collecting certifiable evidence from the pilots' infrastructure.
Benefits: Ensure the truthfulness of the collected data and ease the management of evidence produced by monitoring and assistance with compliance to certification standards.
Differentiator: Component architecture tailored to supply chains needs focussing especially to regulatory obligations (e.g., GDPR) and violations/compliance of service level agreements
KER5 Security & Privacy Dataspace Infrastructure (SPI)
Functionality: Organizing data related to infrastructure events and enforcing privacy and Access Control rules, including Identity Management
Benefits: Secure data transfer between monitored infrastructure and FISHY platform, with data anonymization
Differentiator: An enhanced framework for system events' management, including metrics from different sources and promoting co-relation with added semantics
KER6 Enforcement & Dynamic Configuration (EDC)
Functionality: Translation of high-level policies into low-level configurations for a variety of NSFs (security controls)
Benefits: Adding a new NSF type requires only describing its capabilities using a very simple model
Differentiator: Framework leveraging a capability model instead of the traditional refinement techniques based on logic rules
KER7 Secure Infrastructure Abstraction (SIA)
Functionality: Model-based support for data aggregation and preprocessing: normalization, filtering, etc.
Benefits: Abstract interface allowing the execution of mitigation actions on different types of underlying infrastructure (IoT, IaaS, baremetal, etc)
Differentiator: Data source and consumer dynamic management based on metadata
Projects/Provider:
Resources for EU Research
Resources for SMEs
News & Events
Reports
Cyberwatching.eu has received funding from the European Union’s Horizon 2020 research and innovation programme under grant agreement No 740129. The content of this website does not represent the opinion of the European Commission, and the European Commission is not responsible for any use that might be made of such content. Privacy Policy | Disclaimer / Terms and Conditions of Use
