
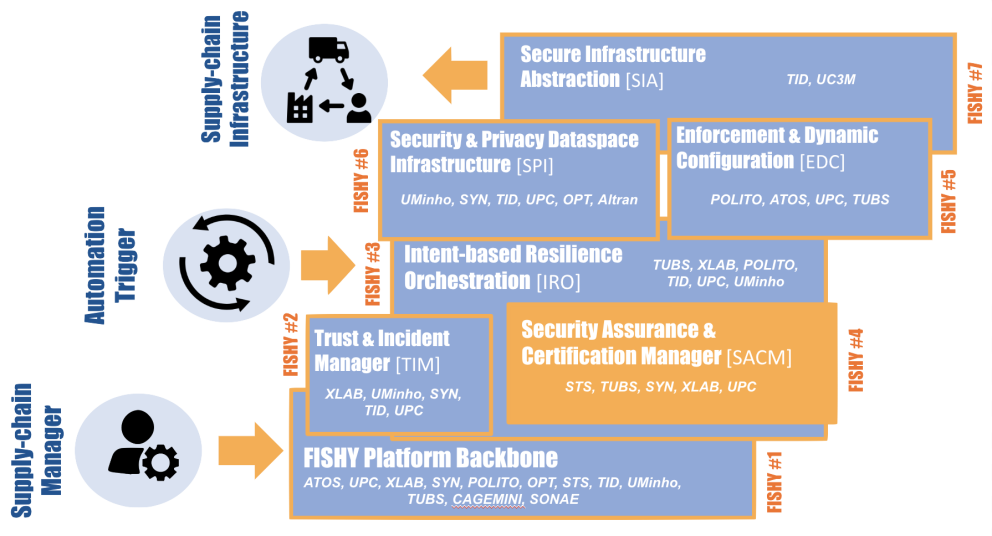
FISHY Security Assurance & Certification Manager

Component architecture tailored to supply chains needs focussing especially on regulatory obligations (e.g., GDPR) and violations/compliance of service level agreements
This technology allows collecting certifiable evidence from the pilots infrastructure, and auditing/reasoning security metrics tailored to the pilots infrastructure. It offers a framework leveraging a capability model instead of the traditional refinement techniques based on logic rules.
BENEFITS
1. Audit component : The custom-based rules are described using a high level language named Event Calculus logic.
2. Event collection engine : uses the Elasticsearch stack (Elasticsearch-logstash-kibana) as main pool of data collection. However it can connect with other (external) data pools using AMQTP technologies (message brokers)
3. The Audit component is integrated in Drools rules management system.
USE CASES
Smart manufacturing - Check if the volume of telemetry is lower as the minimum historic and communicate to analyze impacts.
Autonomous driving - Certify the software versions installed on each vehicle managed on the FISHY platform, and obtain the installed devices from the vehicles and the list of versions certified as safe by the manufacturer. It will compare the version with the listing. When it does not match, the module is expected to send a message to the SADE REST API to control the risk.
Farm-to-fork - It will decide whether the security rules defined by the IT systems' operators have been violated or not in a certain timeframe and provide details about any incident detected based on this rules as well as about policies that have been enforced as a response to an incident.
Horizon Results Platform ID 42333
| Attachment | Size |
|---|---|
| 1.76 MB | |
| 1.03 MB |
Resources for EU Research
Resources for SMEs
News & Events
Reports
Cyberwatching.eu has received funding from the European Union’s Horizon 2020 research and innovation programme under grant agreement No 740129. The content of this website does not represent the opinion of the European Commission, and the European Commission is not responsible for any use that might be made of such content. Privacy Policy | Disclaimer / Terms and Conditions of Use
